Scary new Google Chrome malware attack starts when you see this error message — don't click, millions warned

Researchers from Proofpoint have identified a new technique employed by hackers to coerce PC owners into installing malware onto their machine
|MICROSOFT PRESS OFFICE | PROOFPOINT | GBN

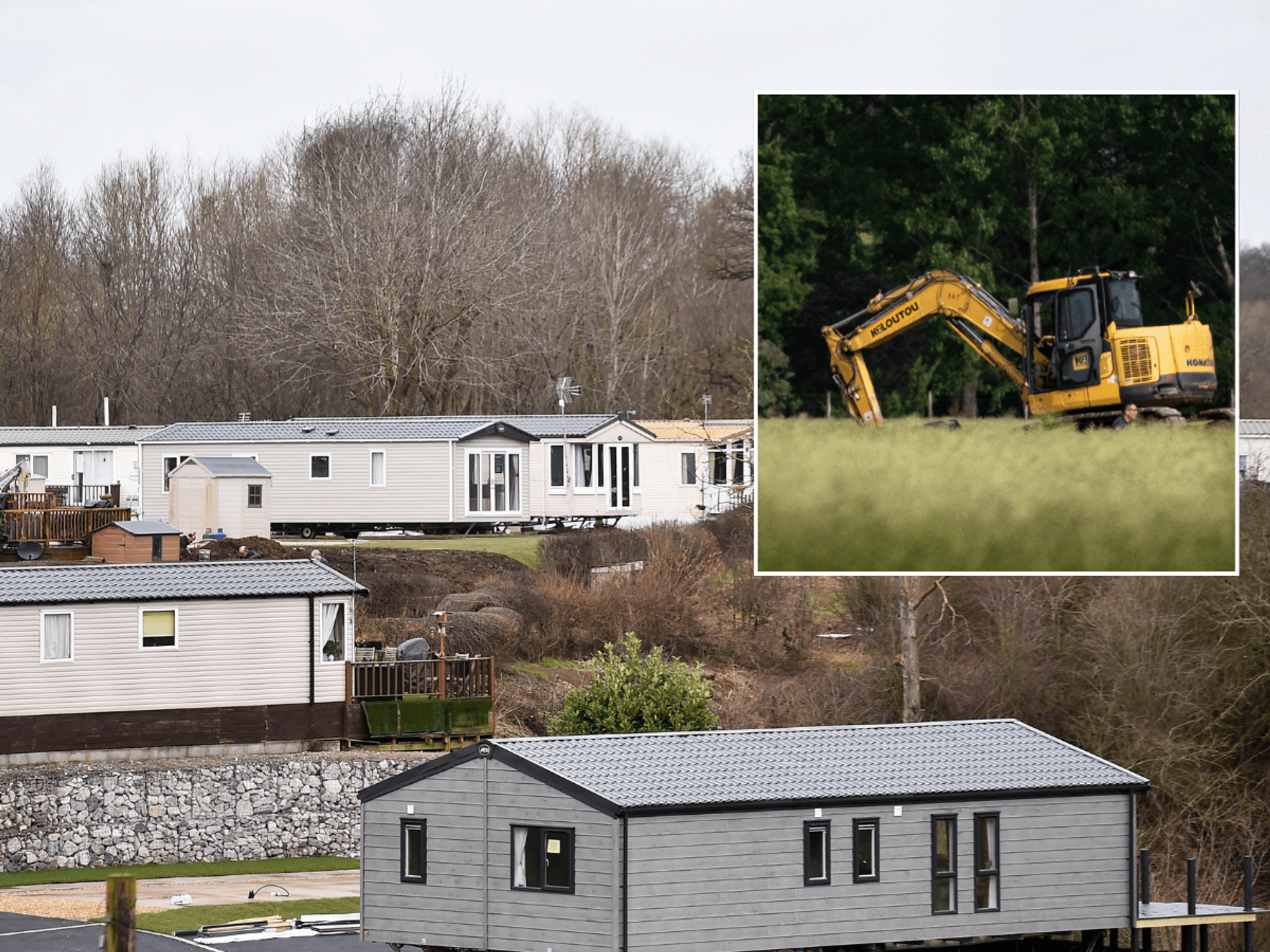
Be wary of pop-ups in Google Chrome and Microsoft Word, researchers caution
- Hackers use a fraudulent error message to trick users into action
- Following the on-screen instructions will trigger a malware attack
- It could allow scammers to redirect your money into their account
- Terrifying attack targets Google Chrome and Microsoft Word users
Don't Miss
Most Read
Latest
Taking action to fix your Google Chrome browser could be the catalyst that infects your PC with malware, millions of users have been warned by new research.
Experts from cybersecurity firm Proofpoint have discovered a dangerous campaign that poses as a fake update within your Google Chrome web browser to coerce you into downloading harmful code. Following the steps outlined in the fraudulent pop-up will unleash a Trojan Horse-like attack on your PC.
Hackers can then trawl through the personal data saved on your desktop PC or laptop, the researchers outline in a detailed blog post about the newly-unearthed attack.
Security experts have uncovered a few examples of fraudulent Google Chrome pop-ups encouraging web browser users to paste malicious code into a terminal window on their machine
|PROOFPOINT
Worse still, malicious software can be deployed to redirect any cryptocurrency sent from your PC into the pockets of the hackers, security experts warn. Proofpoint researchers have not revealed how much money they believe has been stolen from PC owners worldwide using this technique.
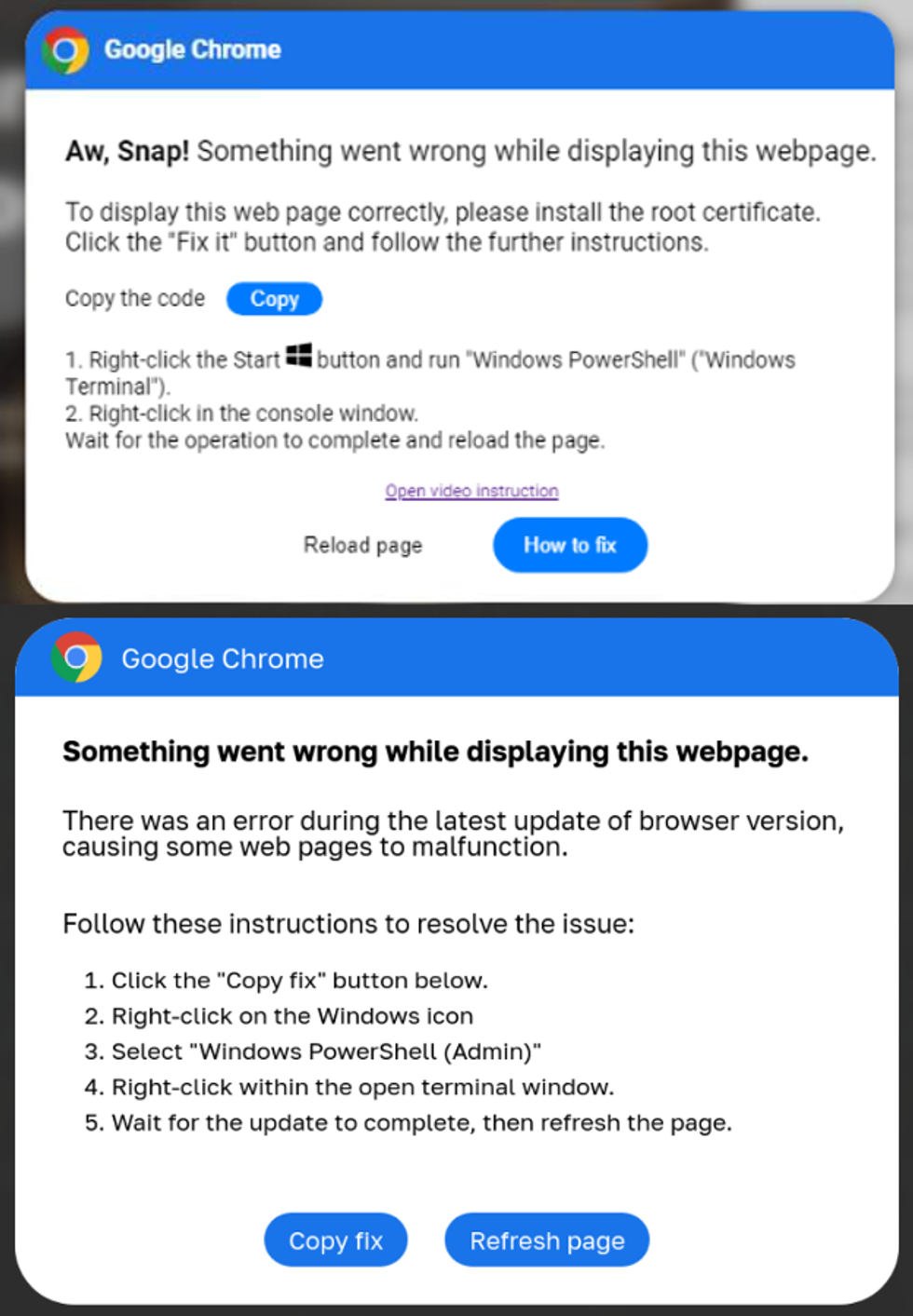
"Aw, Snap! Something went wrong while displaying this webpage," one example of the fraudulently pop-up message discovered by security experts reads. "To display this webpage correctly, please install the root certificate. Click the 'Fix it' button and follow the further instructions."
Another reads: "Something went wrong while displaying this webpage. There was an error during the latest update of browser version, causing some web pages to malfunction."
Both fraudulent pop-ups encourage users to copy the malware code with the tap of a button, launch Windows Powershell (Admin) — a preinstalled app to enable users to control and automate parts of the operating system — from the Start menu, paste the malicious code, and run it within the terminal window.
Put another way: it's a step-by-step guide that teaches Windows users to execute the attack themselves.
This technique of using "fake error messages," warned the researchers, "is clever and purports to be an authoritative notification coming from the operating system."
Any individual or application that instructs you to execute unfamiliar code within a terminal or shell should ring alarm bells, researchers advised. This deep level of system access allows hackers to cause huge damage.
And it's not only Google Chrome users who should be wary of this type of attack. Proofpoint researchers have discovered evidence of a very similar attack targeted at Microsoft Word users.
The malicious pop-up is designed to look like a legitimate warning from Microsoft and — just like the attack aimed at Google Chrome users — will push unsuspecting users into pasting code into a terminal.
"The 'Word Online' extension is not installed in your browser. To view the document offline, click the 'How To Fix' button," one example of these fraudulent warnings reads.
Although the browser-based version of Microsoft Word works across all platforms, the hack is designed specifically for the Windows operating system. As such, only those with Windows 10 or Windows 11 will be impacted by the latest campaign from hackers.
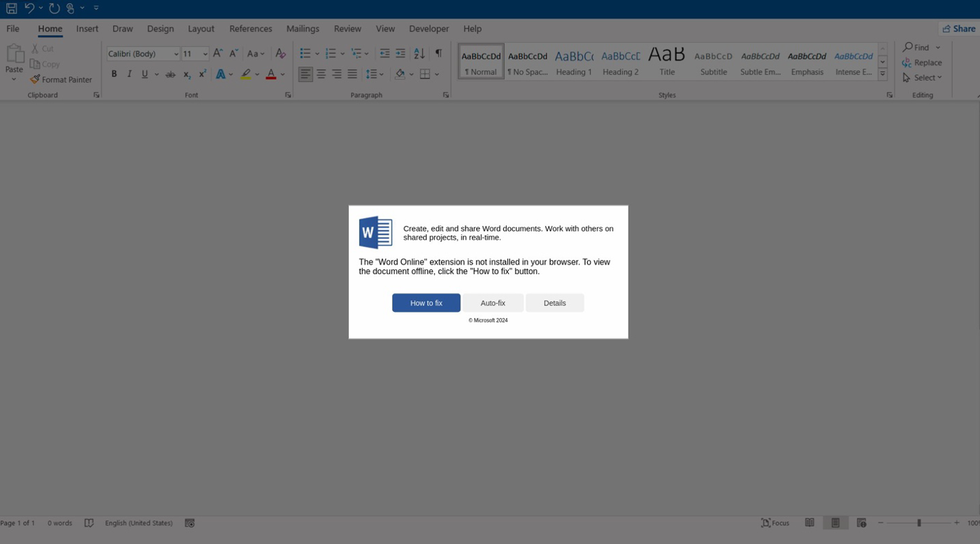
Another example of this type of attack, highlighted by the researchers from Proofpoint, takes aim at people who use Microsoft Word in their browser
|PROOFPOINT
Researchers point out that this attack "requires significant user interaction to be successful," which could limit its impact worldwide. Proofpoint researchers add: "Organisations should train users to identify the activity and report suspicious activity to their security teams.
"This is very specific training but can easily be integrated into an existing user training program."
LATEST DEVELOPMENTS
- Urgent Windows flaw allows hackers to infect your PC over Wi-Fi
- Apple ruthlessly mocks Microsoft over delayed Recall feature
- Millions of iPhone owners will miss out on free AI upgrade from Apple
Applications will Google Chrome and Microsoft Word will never prompt you to manually input code into another application to unlock features. If any of the above pop-up warnings — or similar instructions — appear on your PC, approach with severe caution.